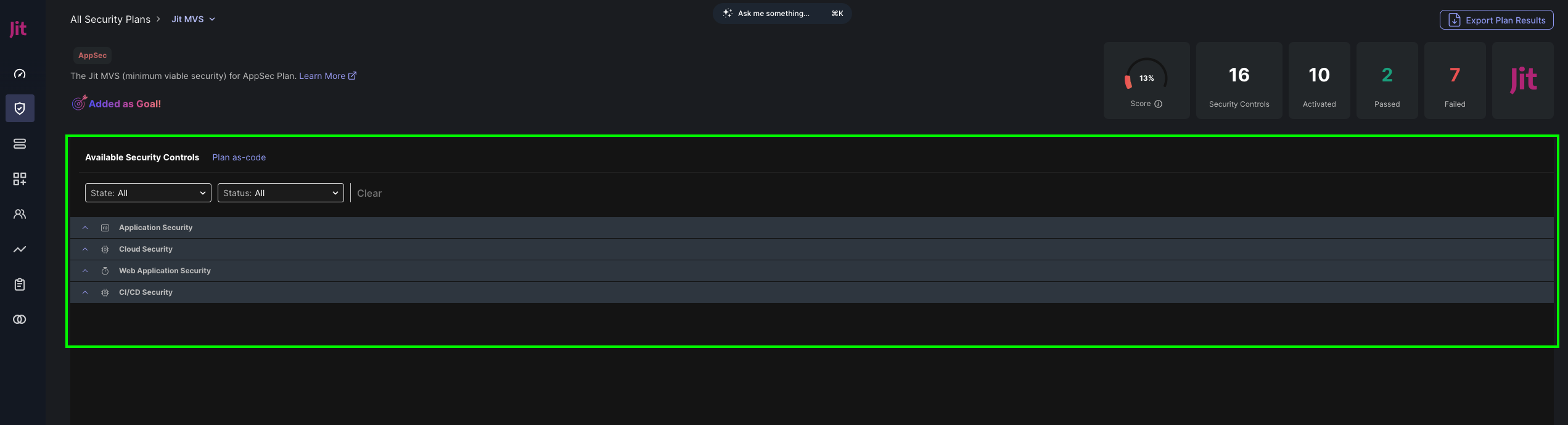
Specific Plan Page
The Jit platform has a page for each security plan:
- Each security plan has a similar structure.
- Security requirements can be activated and configured for each plan.
For a list of all security plans, see Product Security Plans. For more details about Jit security plans, controls, and tools, see Security plan reference.
Plan structure
Plan summary
This section displays:
- Plan version and description.
Set as Goal, Jit streamlines your progress with automated control activation and targeted recommendations.Export Plan Results, use this option to download an.xlsxfile, to be used as a Compliance report.- Widgets, to see the total score, requirements, and findings.
Security Controls (requirements)
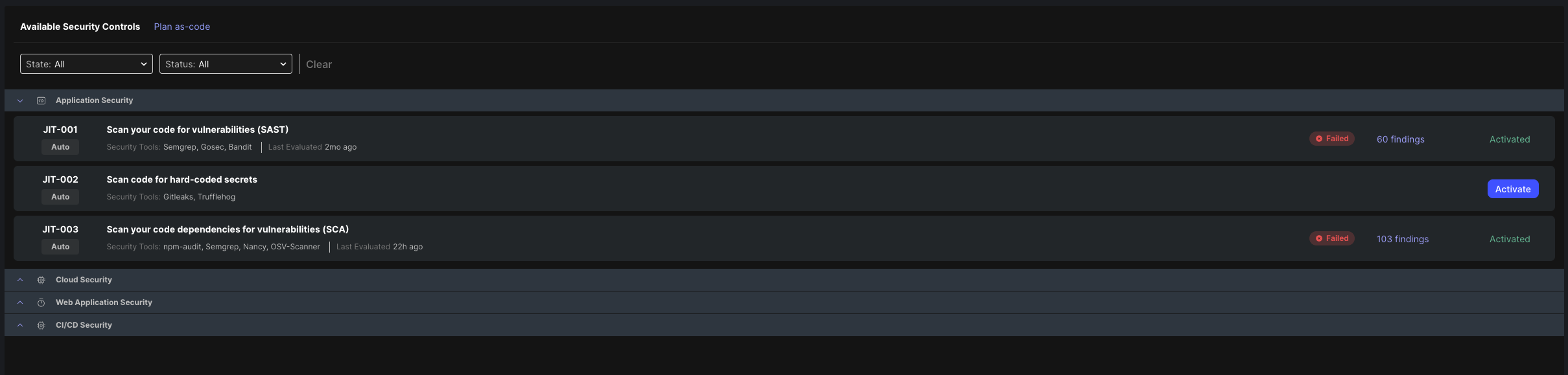
Security plan list of security controls
- Filter by Activation state and pass/fail/error/pending status (based on the security findings).
- Jit identifier per control with a notion indicating whether this control is automatic or manual.
- Automatic controls might require user input (configuration) to run.
- Manual controls, users must set the status of the control manually.
- Security control names and the security tools they run with the last evaluated time. Learn more on Security Controls and Security Tools.
- Each activated security control has a status and a link to all the relevant security findings detected by it.
- To be activated, some security controls need configurations or integrations. For example,
Scan infrastructure for runtime misconfigurationsrequires integration with your organization's cloud provider. - To test a
codesecurity requirement, click Test me to create a test pull request in a pipeline in the Pipelines page. For more test instructions, see Pipelines test.
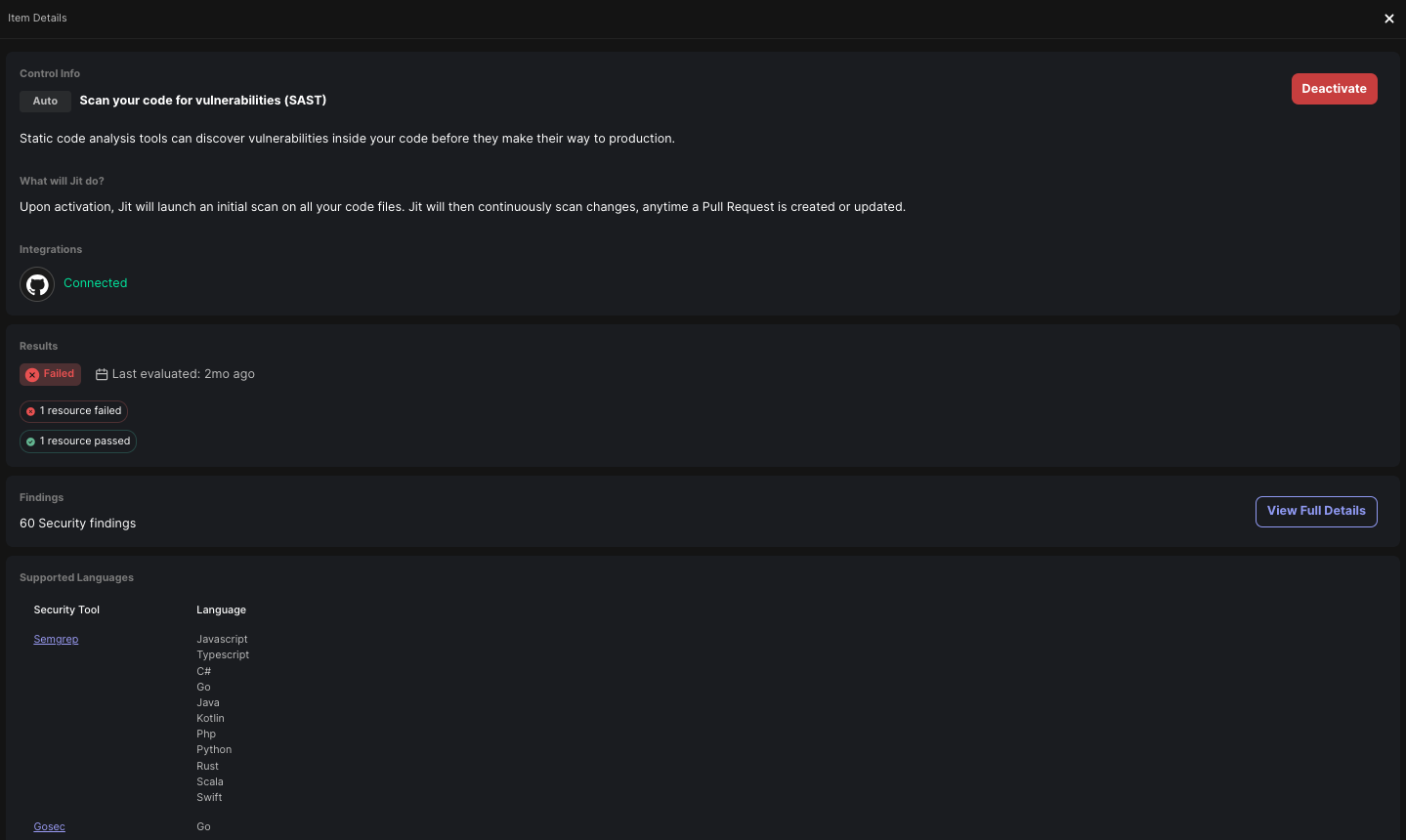
Viewing a security control's (requirement) details
To view more details about a security control, select the control in the table and a right panel will be opened.
Updated 4 months ago
