Scanners Rule Configuration
Default Rules
Jit's SAST scanner uses Semgrep to detect security vulnerabilities in your code. Jit ships a curated ruleset sourced from the Semgrep community rule registry, covering the most impactful security patterns across all supported languages. You can browse the full registry to see what rules are available.
Current Semgrep version: 1.109.0
Supported languages:
| Language |
|---|
| Python |
| Java |
| JavaScript / TypeScript |
| Kotlin |
| Scala |
| C# |
| Swift |
| Rust |
| PHP |
| Ruby |
| C / C++ |
| YAML |
| Bash |
Severity: Jit surfaces HIGH and MEDIUM severity findings. INFO-level findings are not shown.
| Semgrep severity | Jit severity |
|---|---|
| ERROR | HIGH |
| WARNING | MEDIUM |
| INFO | Not shown |
Customizing Your Configuration
You can extend the default ruleset with your own Semgrep rules. Custom rules run alongside Jit's defaults - they don't replace them.
Using the UI editor
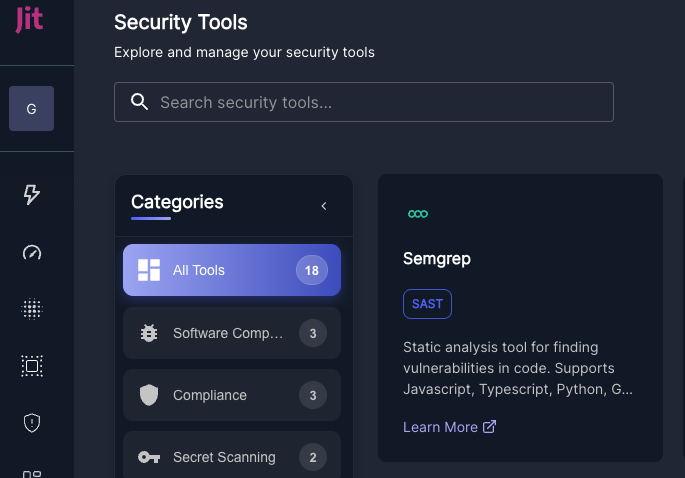
From the Jit platform, go to Settings → Security Tools and open the Semgrep configuration editor.
Enter your rules in standard Semgrep rule syntax and save. You can also upload a pre-configured file from the same page.
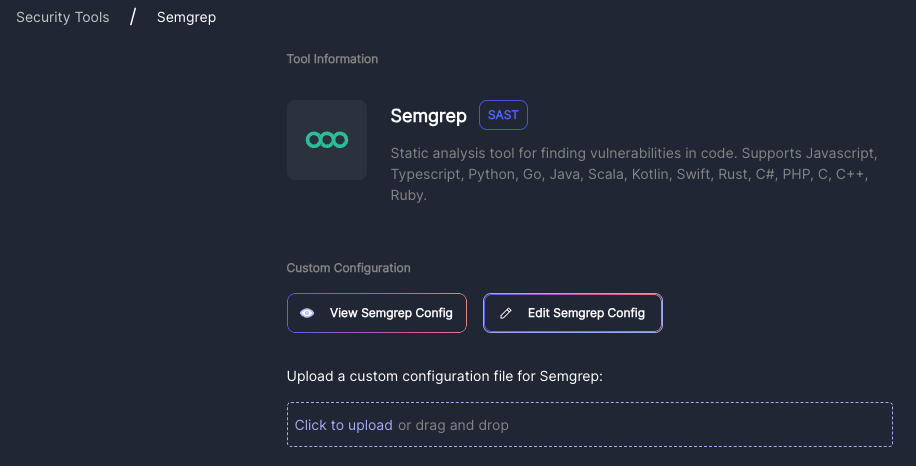
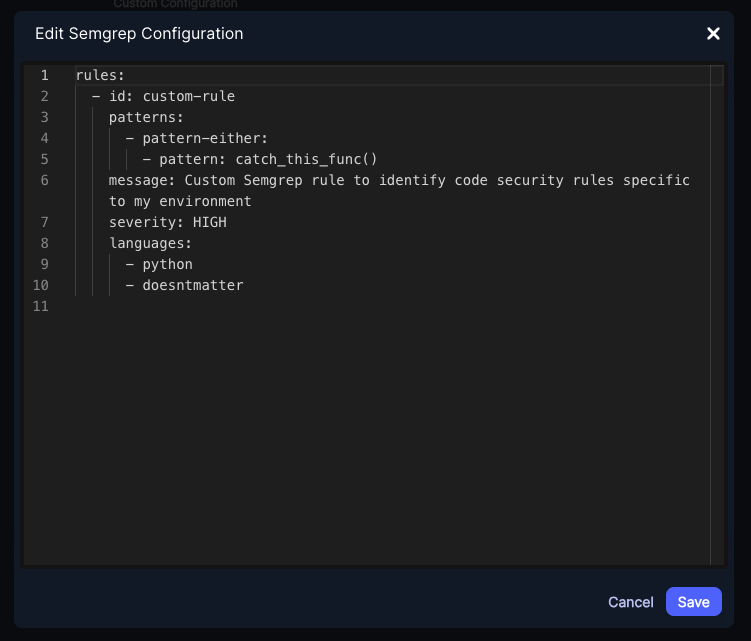
Changes take effect on the next scan.
Semgrep Pro
If your organization has a Semgrep Pro subscription, you can use it in Jit instead of the default scanner for deeper inter-procedural and taint analysis. See Semgrep Pro Tier Integration.
Updated 3 months ago
